6G wireless technology could use humans as a power source, study explains
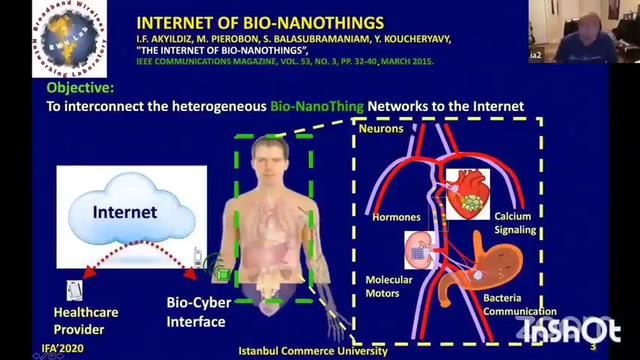
5G wireless technology is just starting to take off worldwide, but a new study is already speculating on the future of 6G! Researchers from the University of Massachusetts-Amherst say, unlike older technology, 6G could end up using people as antennas.
Specifically, 6G telecommunications could possibly take advantage of Visible Light Communication (VLC), which is like a wireless version of fiberoptics. Right now, fiberoptics use incredibly thin glass or plastic strands to transmit information on flashes of light. These wires are extremely small, but also extremely fragile.
The UMass Amherst team says they have created a low-cost and innovative way of harvesting waste energy from VLC — using the human body as an antenna. Their invention can recycle waste energy to power wearable devices and possibly larger electronics as well.
“VLC is quite simple and interesting,” says Jie Xiong, professor of information and computer sciences at UMass Amherst, in university release. “Instead of using radio signals to send information wirelessly, it uses the light from LEDs that can turn on and off, up to one million times per second.”
What makes VLC so appealing to the future of wireless technology is the fact that the infrastructure to use it already exists. Thanks to modern technology and smart devices, our homes, vehicles, streetlights, and offices are all lit by LED bulbs, and they could also be transmitting data.
“Anything with a camera, like our smartphones, tablets or laptops, could be the receiver,” Xiong explains.
6G could rely on VLC ‘leakage’
The team explains that VLC systems experience a significant “leakage” of energy because LEDs emit “side-channel RF signals” — or radio waves. If scientists are able to harvest this RF energy, they can put it to use.
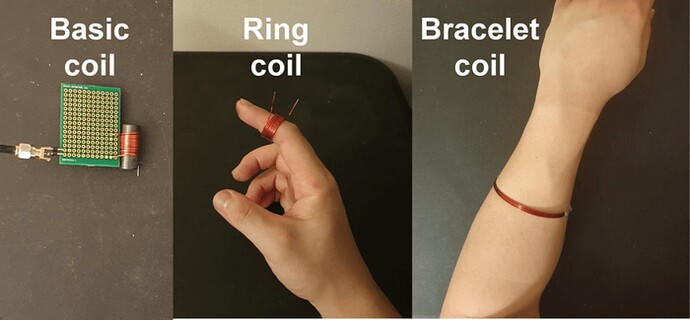
To turn this into reality, they designed an antenna out of coiled copper wire to collect leaked RF. From there, the biggest question is what kind of object maximizes the collection of this energy?
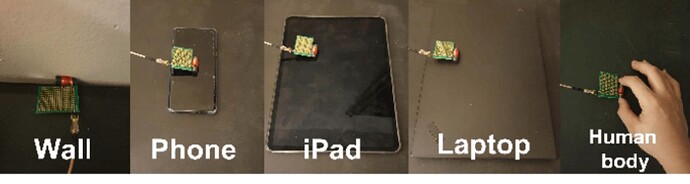
Researchers experimented with all sorts of surfaces and thicknesses of wire. After resting the coil against plastic, cardboard, wood, and steel, as well as phones and other digital devices turned on and off, first author Minhao Cui tried wrapping the coil around a human body.
The team experimented using different daily objects to amplify the harvested power, and discovered that the human body is one of the best materials. CREDIT: Cui et al., 10.1145/3560905.3568526
Results show people are actually the best medium for amplifying the coil’s ability to collect leaked RF energy. Attaching the coil to a person collected up to 10 times more energy than just using a bare coil.
A cheap bracelet could give you 6G service
Based on these results, the researchers created an inexpensive, wearable device called the “Bracelet+,” which people can wear on their upper forearm. Study authors note they can even modify it to work as a ring, belt, anklet, or necklace — although a bracelet seemed to work best for harvesting power.
Different coil designs influence the amount of power harvested. CREDIT: Cui et al., 10.1145/3560905.3568526
“The design is cheap—less than fifty cents,” the study authors note. “But Bracelet+ can reach up to micro-watts, enough to support many sensors such as on-body health monitoring sensors that require little power to work owing to their low sampling frequency and long sleep-mode duration.”
“Ultimately, we want to be able to harvest waste energy from all sorts of sources in order to power future technology,” Xiong concludes.